when deploying 2g defense servers in cambodia and other places, it is difficult for a single protection method to deal with complex application layer attacks and traffic bursts. combining waf and traffic scheduling can form a collaborative defense, which not only improves the detection and interception capabilities of malicious requests, but also optimizes resource allocation and availability, significantly improving the overall defense effect and operation and maintenance efficiency. this article puts forward feasible suggestions from a technical and implementation perspective, which are suitable for localized network environments and seo search optimization needs.
the cambodian network environment is characterized by unstable links, limited bandwidth, and dispersed equipment distribution, making it difficult for traditional border protection to cover application layer threats. 2g networks still carry a large number of iot and voice services, making them easy targets for attacks such as ddos and injection. therefore, combining application layer protection and scheduling strategies can help improve business availability, reduce false alarms, reduce local bandwidth waste, and meet local geo search and compliance requirements.
waf (web application firewall) is mainly positioned at application layer threat protection and has the ability to identify and intercept sql injection, cross-site scripting, abnormal request behavior, etc. in 2g defense scenarios, waf can be used as the first line of defense to filter malicious http/https traffic, block vulnerability exploit links, cooperate with adaptive rules and machine learning-based behavioral analysis, reduce the impact on core network resources, and provide cleaned traffic statistics for traffic scheduling.
when deploying waf in cambodia, static rules and behavioral analysis should be combined: static rules cover known vulnerabilities and attack patterns, and behavioral analysis identifies abnormal sessions and sudden access. it is recommended to regularly update the rule base, enable geographical and time policies, and combine whitelisting and rate limiting to avoid accidentally blocking legitimate 2g terminals. adjust strategies through log and indicator feedback to ensure adaptability to local traffic characteristics.
traffic scheduling distributes user requests to multiple protection or application instances through intelligent offloading and load balancing, alleviating single-point bottlenecks and improving redundancy. during an attack, the scheduling layer can cooperate with health checks, circuit breakers, and back-to-source control to isolate abnormal traffic to cleaning nodes or throughput-limited paths to ensure that core services continue to be available. for cambodia's 2g environment, reasonable scheduling strategies can reduce link congestion and improve user experience.

intelligent offloading relies on real-time traffic analysis and preset policies to direct suspected attack traffic to waf or cleaning clusters, while adjusting bandwidth allocation according to business priorities. peak mitigation can use traffic absorption, rate limiting and hierarchical rollback strategies, combined with grayscale rollback and downgrade services when necessary, to ensure priority for key voice or iot services and reduce the scope of the overall fault impact.
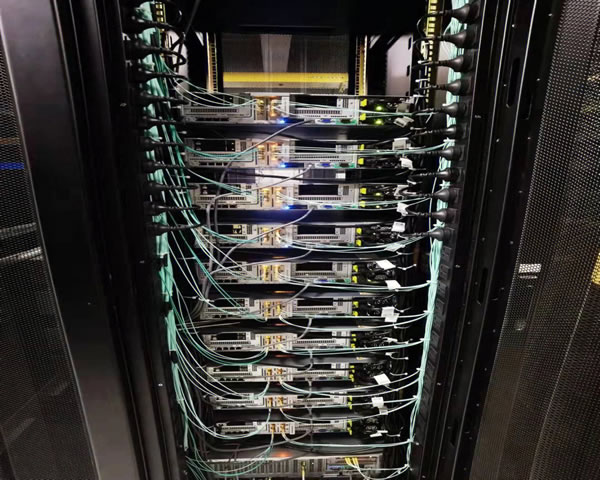
achieving synergy requires unification in architecture and configuration: first, introduce waf fingerprint and blacklist synchronization at the scheduling layer; second, connect waf logs and scheduling links to support real-time decision-making; third, establish policy priorities to avoid repeated blocking that affects legitimate traffic. deployment location (edge, regional or central) and failover strategies also need to be considered to adapt to cambodia's local network topology and bandwidth characteristics.
continuous monitoring and drills are key: it is recommended to establish a visual dashboard including traffic, sessions, false alarm rates and delays, and regularly drill peak cleaning and failover. set abnormal alarm thresholds based on local traffic baselines, and implement compliance log storage policies and privacy protection together. the operation and maintenance team should have the ability to quickly tune rules and adjust scheduling strategies to ensure response time and recovery capabilities.
summary: combining waf and traffic scheduling can significantly improve the overall effect of cambodia's 2g defense server, taking into account interception capabilities and availability. during implementation, attention should be paid to policy coordination, log unblocking and local network adaptation, together with continuous monitoring and drills, to achieve stable and reliable protection and high-quality user experience. it is recommended to verify the strategy on a small scale first, and then gradually promote it to the entire network.
- Latest articles
- User Reputation Summary And Analysis Of The Latest Trends In The Top Ten Rankings Of Us Cloud Servers
- Analysis Of The Impact Of Malaysian Servers On Search Results From The Perspective Of Marketing And Seo
- Guide To The Customization Service Process And Delivery Cycle Of Us High-defense Servers Under Customized Needs
- How Can Enterprise Users Uniformly Manage Japanese Native Ip Login Entrance And Permission Control?
- Logistics Risk Assessment: Can Physical Servers Be Shipped To Thailand? Packaging And Insurance Recommendations
- Choose Taiwan Vps Native Ip Physical Machine To Deploy Exclusive Bandwidth And Stable Connection Solution
- Case Sharing Of Cambodia’s Real Experience Of 2g Defense Server Successfully Resisting Attacks
- Comparison Of The Advantages And Disadvantages Of Vietnam's Native Ip Vps Hosting And Self-management To Help You Choose The Appropriate Operation And Maintenance Model
- Network Optimization Techniques For Taiwan Server Game Cloud Hosts When Deploying Cross-region Matching Services
- It Is Recommended To Plan The Costs And Benefits Of Overseas Expansion Based On The Investment Budget. Does Tencent Cloud Have Korean Servers?
- Popular tags
-
Why Choose Cambodia CN2 As The First Choice For Returning Servers
This article discusses the advantages of choosing Cambodian CN2 as a return server, analyzes its network performance, data security and applicable scenarios, and provides users with comprehensive selection suggestions. -
Exploring Cambodia Server Addresses And Their Advantages
Uncovering Cambodia server addresses and their advantages, understanding how Cambodia servers can enhance website performance and optimize search engine rankings. -
Tips For Improving Network Speed Using Cambodian CN2 Return Server
This article introduces skills to use Cambodian CN2 return server to improve network speed and helps users optimize network experience.